Security center
Actionable security insights for G Suite
- Protect your organization with security analytics and best practice recommendations from Google. The security center is included with G Suite Enterprise edition.
Actionable security insights for G Suite
Get insights into external file sharing, visibility into spam and malware targeting users within your organization, and metrics to demonstrate your security effectiveness in a single, comprehensive dashboard.

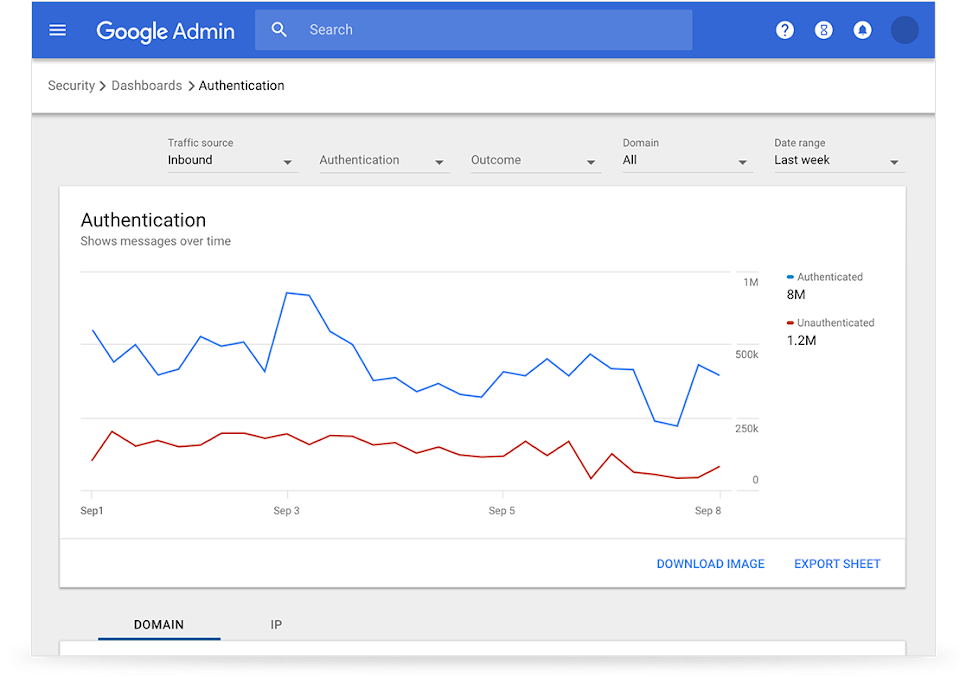
Analyze email messages that do not meet your organization's authentication standard. Proactively gain insights on which Drive files are triggering Data Loss Protection (DLP) rules and determine the course of action against potential data exfiltration.
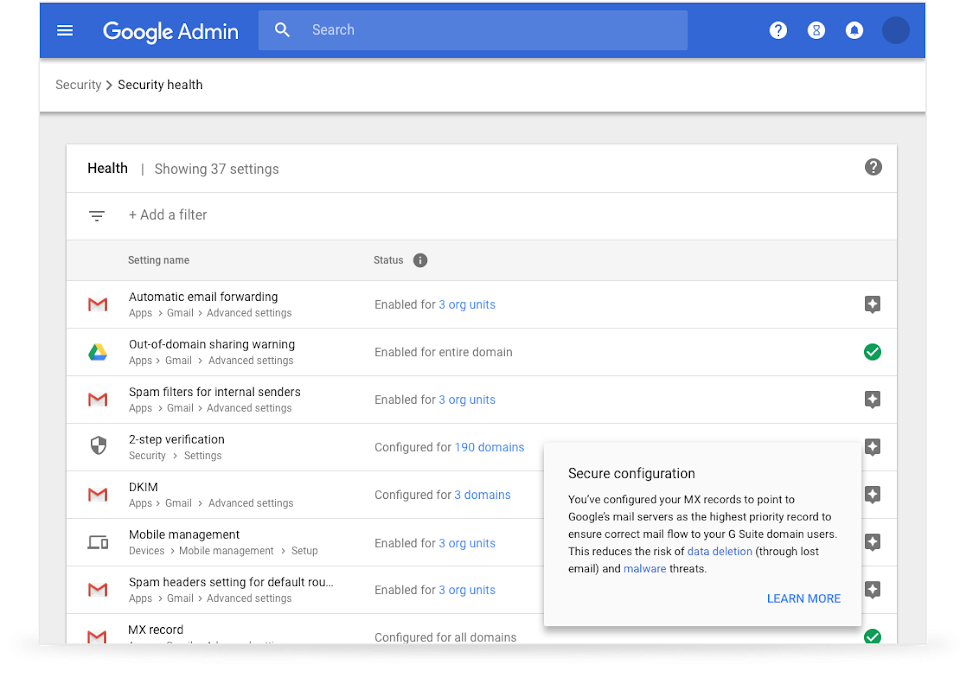
Stay ahead of threats with the quickstart guide, which provides recommended security settings and gives customized advice on security best practices for content, communication, mobility, and user security.
Understand which files have been shared outside your domain and which shared files have triggered DLP rules.
Find out how many messages don’t meet authentication standards, like DMARC, DKIM, and SPF.
Ensure that messages sent by your domain are encrypted using TLS.
See what percentage of incoming messages were accepted and whether whitelisting allowed suspicious messages to get delivered.
Analyze messages deemed to be spam, phishing, suspicious, or containing malware.
Evaluate whitelists by reviewing whether users have tagged delivered messages as spam or phishing.
Set security checks on automatic email forwarding, DMARC settings, POP/IMAP access, and whitelists.
Apply policies for file sharing, Drive add-ons, offline availability, and stringent sign-in requirements.
Get a comprehensive action list for Mobile Device Management policies.
Gain visibility into how 2-step verification is being used across users and admins.
Check whether out-of-domain warnings are in place for all users.
Review group sharing options and evaluate public groups on a case-by-case basis.